While studying asmap, I could understand that Core tries to connect to at most one peer per AS, like:
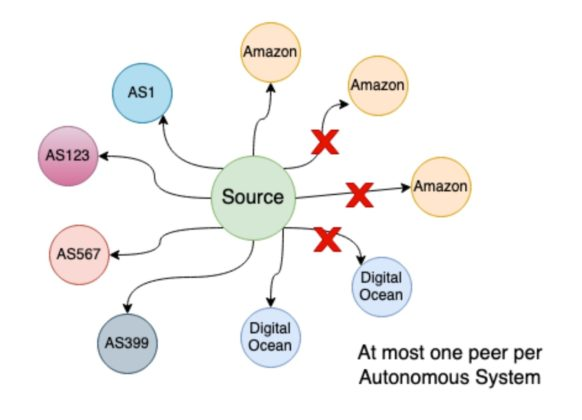
Supposing I don't want to have my node connected to Amazon or Digital Ocean, doesn't it make sense to make possible to set up my node to avoid connecting to certain AS (something like -asmapavoid=abc,bca,cba...?