Is your feature request related to a problem? Please describe.
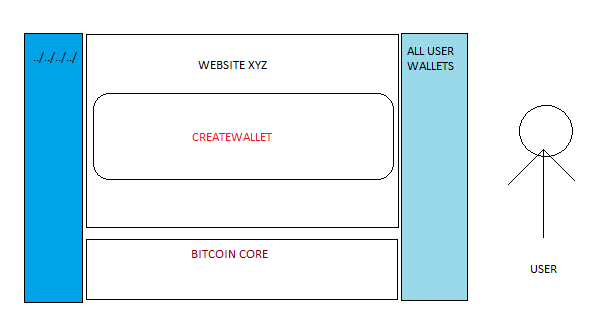
Wallets with weird names possible which can be exploited in vulnerable web applications that use Bitcoin Core and allow the users to create and import/export wallet
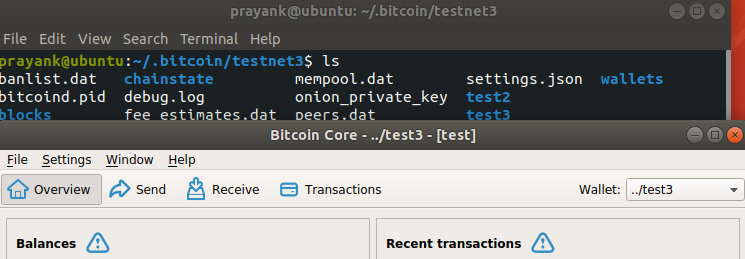
../testwallet for Linux
..\testwallet for Windows
Tried on Bitcoin Core v 0.20.0
Describe the solution you'd like
Keep two arguments:
wallet_nameandwallet_pathforcreatewalletfilenameandfilepathfordumpwalletimportwalletValidate user input. Name should not contain special characters. Path should be optional and if not specified use a default value.
Describe alternatives you've considered Web developers should create secure web apps that use Bitcoin Core.
Additional context
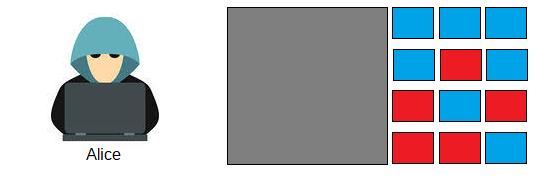
I understand its not a vulnerability in Bitcoin Core and only affects vulnerable web apps that use Bitcoin Core. However we can at least consider it a bug that may affect something in future or other projects that use Bitcoin Core. Basic checks for user input can improve the security. In 2017 I had a website in which someone had reported a vulnerability that could be used to change price of flight tickets and book with almost zero bitcoin. It was an issue with the website and we had to fix it although nobody could exploit it because the third party APIs that we were using to book the fight tickets were validating all the things. So a ticket couldn't be processed after tampering and changing the price by attacker. Similarly, if any web developer makes a mistake and using Bitcoin Core for the web app would still be unaffected if Bitcoin Core itself doesn't allow such things for wallet names.
There have been lot of directory traversal related vulnerabilities, recently one was reported in Facebook android app:
https://portswigger.net/daily-swig/vulnerability-in-facebook-android-app-nets-10k-bug-bounty