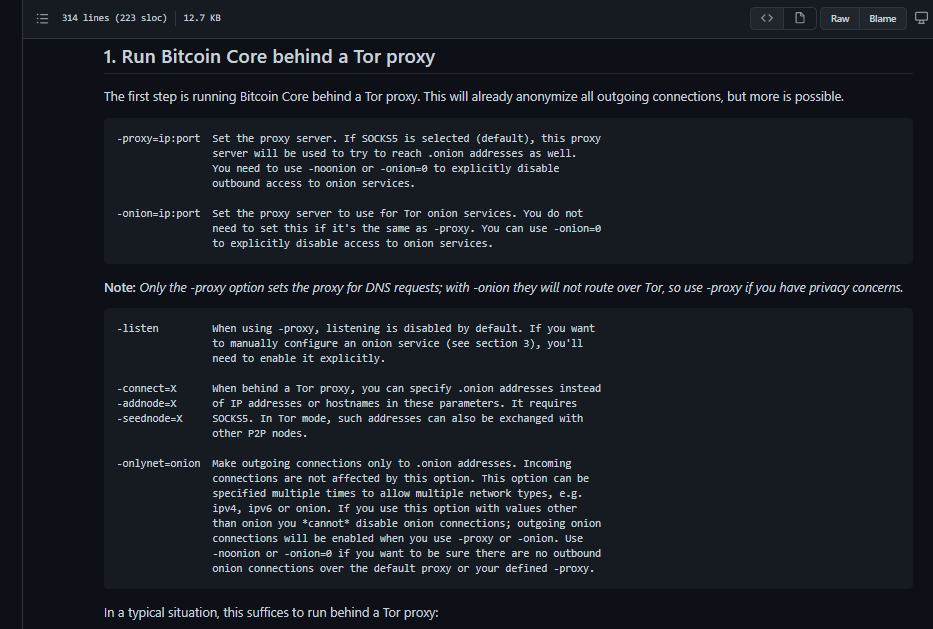
- Highlight the part which mentioned about DNS requests and Tor usage
- Add an example to make it easier for normal users or even power users to ignore all the other details and try basic setup first to avoid confusion
- Add 4 privacy recommendations
- About usage of Tor and Tor bridges, suggestions to consider tradeoffs based on user environment.
- Mention about Deleting "onion_v3_private_key" frequently doesn't help and for some users its better to not use Bitcoin Core Onion Service.
- Trade-offs involved in using
onlynet=onion - Downloading packages using
torsocksContext: #20757 (review)
Reasons:
- Point mentioned about DNS requests is important. I am not sure if we can include more details in this doc but it should be highlighted. I had asked one related question recently on Reddit: https://www.reddit.com/r/Bitcoin/comments/l641hj/dns_requests_in_bitcoin_core/
- Usage of Tor and Tor bridges is not same in all places. Users should be aware of such things.
- Adding an example makes it easier for normal users to refer this doc when they try Bitcoin Core Onion Service first instead of reading several other articles, thread, questions etc. on different websites. Recently someone tweeted a thread about installing Bitcoin Core: https://twitter.com/Ethan_Heilman/status/1355645616056098817
Fixes #19923