This PR fixes #23589
This PR adds a new utility function, TorControlArgumentCheck, which can be used to check if a given string is a valid <host>:<port> pair or not.
This PR also uses this new function to check the validity of the -torcontrol argument and raises an InitError in case the value of this argument is invalid.
| Master | PR |
|---|---|
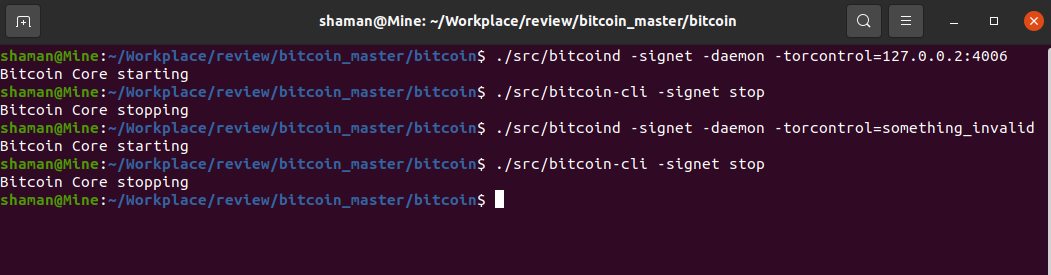 |
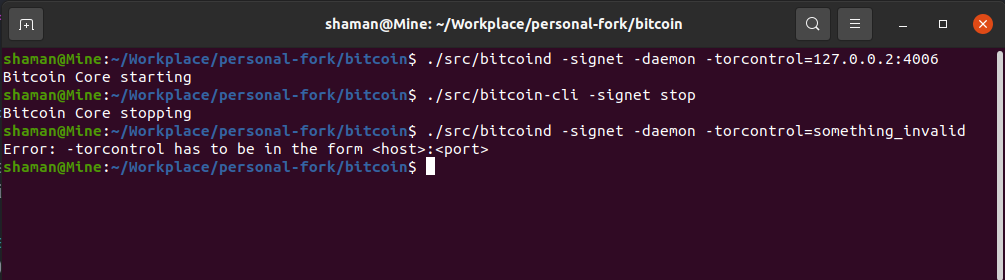 |