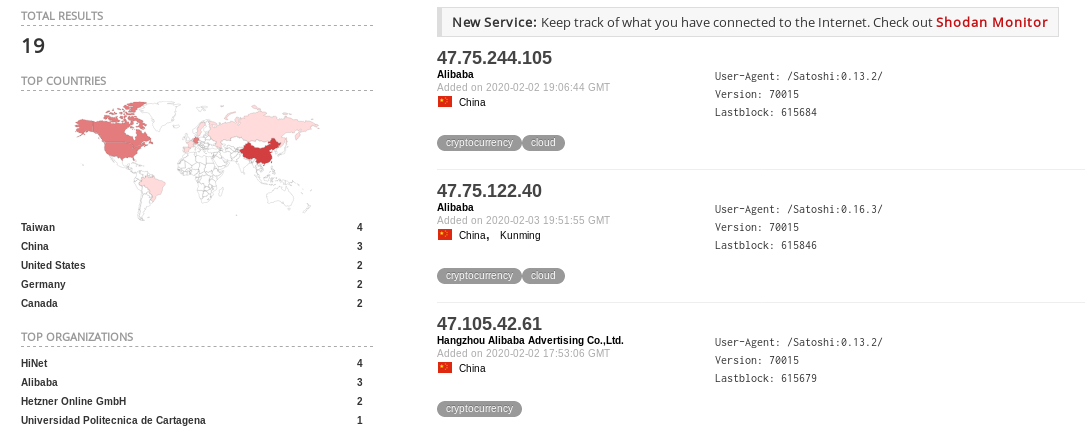
According to public internet scan data, approximately 10% of Bitcoin nodes listening on 8333 also have their RPC port misconfigured to listen on 0.0.0.0. There is no way that this can be used safely which does not involve plaintext credentials being transmitted across the internet, especially since the complete removal of rpcssl. If this is desirable, proxying the socket through nginx with SSL is a viable alternative that does not require listening publically.
The rpcbind option should either be restricted to allow for only single definitions of a host, or removed entirely to only permit binding to localhost for the management interface.