Document how to fuzz Bitcoin Core using Honggfuzz.
doc: Document how to fuzz Bitcoin Core using Honggfuzz #18739
pull practicalswift wants to merge 1 commits into bitcoin:master from practicalswift:honggfuzz changing 1 files +22 −0-
practicalswift commented at 3:24 PM on April 22, 2020: contributor
-
doc: Document how to fuzz Bitcoin Core using honggfuzz bb1ec36fb1
-
MarcoFalke commented at 3:33 PM on April 22, 2020: member
Nice. Concept ACK
- DrahtBot added the label Docs on Apr 22, 2020
-
kiminuo commented at 9:00 PM on April 22, 2020: contributor
Good job. Concept ACK
(bikeshedding: One thing I've just noticed is that commands are prefixed with
$. I find it nice from documentation POV. Although it may be impractical when somebody wants to copy the commands and run them in a batch. Moreover, mostly it looks like other documents indocfolder do not follow this convention - there are no$prefixes for command listings.) - fanquake approved
-
fanquake commented at 11:18 AM on April 25, 2020: member
ACK bb1ec36fb171816309ae5af53d549ff3e4633f67 - did a couple quick runs on a severely under powered VM.
------------------------[ 0 days 00 hrs 17 mins 01 secs ]---------------------- Iterations : 187,722 [187.72k] Mode [3/3] : Feedback Driven Mode Target : src/test/fuzz/p2p_transport_deserializer Threads : 1, CPUs: 2, CPU%: 51% [25%/CPU] Speed : 79/sec [avg: 183] Crashes : 0 [unique: 0, blacklist: 0, verified: 0] Timeouts : 20 [1 sec] Corpus Size : 76, max: 8,192 bytes, init: 837 files Cov Update : 0 days 00 hrs 02 mins 58 secs ago Coverage : edge: 5,116/918,069 [0%] pc: 125 cmp: 114,846 ---------------------------------- [ LOGS ] ------------------/ honggfuzz 2.2 /- ersistent mode: Launched new persistent pid=10224 [2020-04-25T11:00:17+0000][W][10182] subproc_checkTimeLimit():528 pid=10224 took too much time (limit 1 s). Killing it with SIGKILL [2020-04-25T11:00:17+0000][W][10182] arch_checkWait():234 Persistent mode: pid=10224 exited with status: SIGNALED, signal: 9 (Killed) Sz:40 Tm:1,101,025us (i/b/h/e/p/c) New:0/0/0/0/0/3, Cur:0/0/0/0/0/17190 Sz:20 Tm:1,211,777us (i/b/h/e/p/c) New:0/0/0/0/0/578, Cur:0/0/0/0/0/11950 Persistent mode: Launched new persistent pid=10230 [2020-04-25T11:00:23+0000][W][10182] subproc_checkTimeLimit():528 pid=10230 took too much time (limit 1 s). Killing it with SIGKILL [2020-04-25T11:00:23+0000][W][10182] arch_checkWait():234 Persistent mode: pid=10230 exited with status: SIGNALED, signal: 9 (Killed) Sz:64 Tm:1,100,172us (i/b/h/e/p/c) New:0/0/0/0/0/1536, Cur:0/0/0/0/0/16063 Persistent mode: Launched new persistent pid=10231 Sz:89 Tm:241us (i/b/h/e/p/c) New:0/0/0/0/0/2, Cur:0/0/0/338/0/367 Sz:87 Tm:128us (i/b/h/e/p/c) New:0/0/0/0/0/1, Cur:0/0/0/334/0/146 Thread 0 (pid=10231) initial speed set at 4466 us/exec Sz:89 Tm:162,207us (i/b/h/e/p/c) New:0/0/0/0/0/1, Cur:0/0/0/338/0/582 Sz:120 Tm:4,512us (i/b/h/e/p/c) New:0/0/0/0/0/1, Cur:0/0/0/339/0/146 Sz:27 Tm:8,737us (i/b/h/e/p/c) New:0/0/0/0/0/2, Cur:0/0/0/334/0/146 Sz:105 Tm:173us (i/b/h/e/p/c) New:0/0/0/0/0/2, Cur:0/0/0/345/0/369 Sz:33 Tm:8,805us (i/b/h/e/p/c) New:0/0/0/0/0/1, Cur:0/0/0/334/0/146 Sz:168 Tm:224us (i/b/h/e/p/c) New:0/0/0/0/0/70, Cur:0/0/0/347/0/801 -
MarcoFalke commented at 1:21 PM on April 25, 2020: member
Going to merge this, we can improve formatting later on
- MarcoFalke merged this on Apr 25, 2020
- MarcoFalke closed this on Apr 25, 2020
- sidhujag referenced this in commit 65ae410a56 on Apr 25, 2020
-
MarcoFalke commented at 9:38 PM on May 15, 2020: member
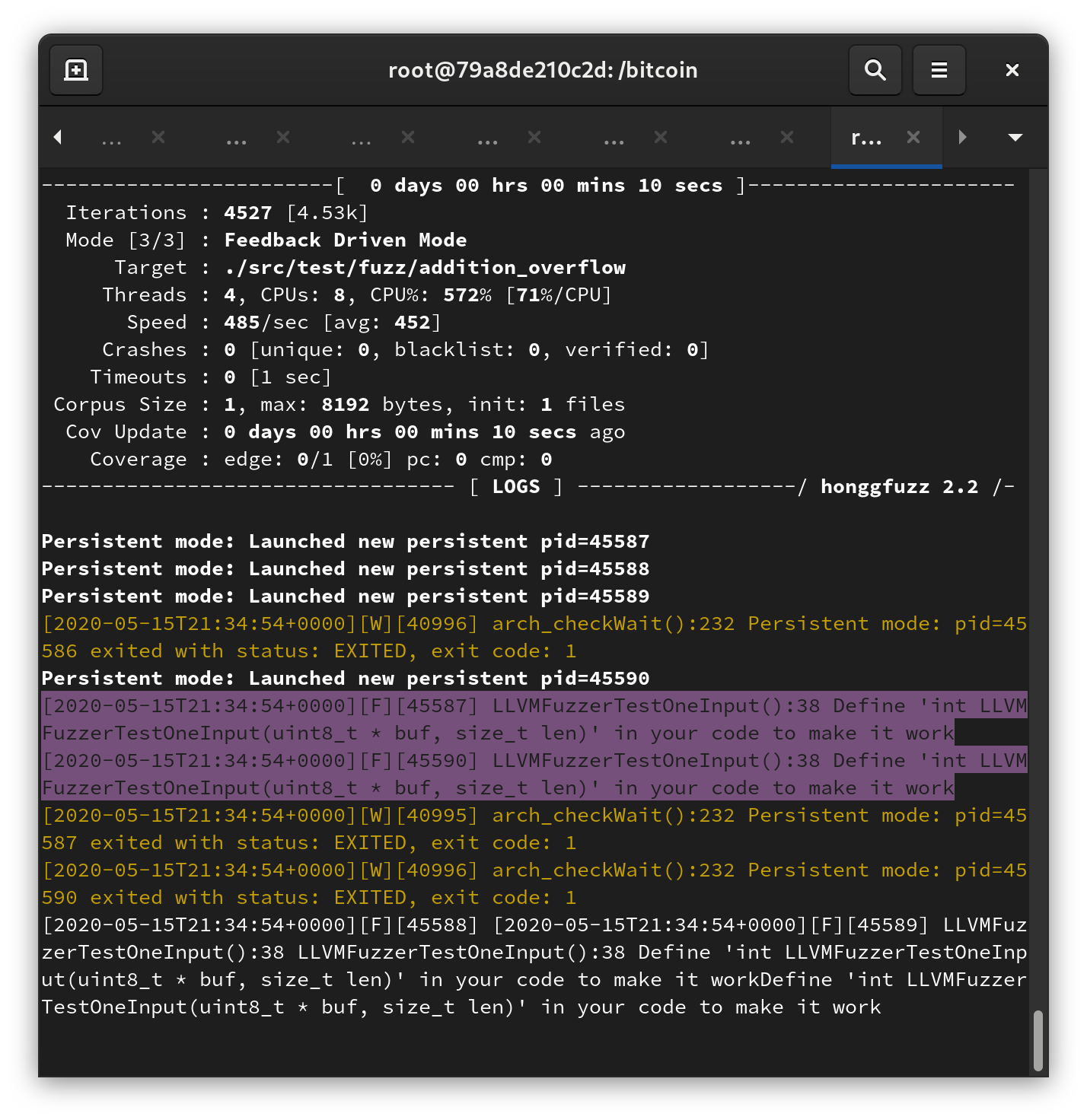
@practicalswift Can you explain how hongfuzz is supposed to work?
I am adding a runtime assert(false) in the first line of the fuzzer, but it won't crash.
diff --git a/src/test/fuzz/addition_overflow.cpp b/src/test/fuzz/addition_overflow.cpp index a455992b1..a14249ed8 100644 --- a/src/test/fuzz/addition_overflow.cpp +++ b/src/test/fuzz/addition_overflow.cpp @@ -42,6 +42,7 @@ void TestAdditionOverflow(FuzzedDataProvider& fuzzed_data_provider) void test_one_input(const std::vector<uint8_t>& buffer) { + assert(false); FuzzedDataProvider fuzzed_data_provider(buffer.data(), buffer.size()); TestAdditionOverflow<int64_t>(fuzzed_data_provider); TestAdditionOverflow<uint64_t>(fuzzed_data_provider);Also, the coverage stays at 0%
-
MarcoFalke commented at 9:38 PM on May 15, 2020: member
The message is:
[2020-05-15T21:37:31+0000][F][48002] LLVMFuzzerTestOneInput():38 Define 'int LLVMFuzzerTestOneInput(uint8_t * buf, size_t len)' in your code to make it work -
MarcoFalke commented at 1:12 PM on May 19, 2020: member
@practicalswift Let me know if my setup is incorrect. But if honggfuzz is unable to find the most trivial bug, it should be removed from the documentation.
-
practicalswift commented at 3:10 PM on May 19, 2020: contributor
That's weird:
LLVMFuzzerTestOneInputshould be defined (it is whatlibFuzzeruses).Does it work better if you apply the following patch and run
honggfuzzwith the-soption (honggfuzz/honggfuzz -i inputs/ -s -- src/test/fuzz/multiplication_overflow)?diff --git a/src/test/fuzz/fuzz.cpp b/src/test/fuzz/fuzz.cpp index 6e2188fe8..6293714f7 100644 --- a/src/test/fuzz/fuzz.cpp +++ b/src/test/fuzz/fuzz.cpp @@ -12,7 +12,6 @@ const std::function<void(const std::string&)> G_TEST_LOG_FUN{}; -#if defined(__AFL_COMPILER) static bool read_stdin(std::vector<uint8_t>& data) { uint8_t buffer[1024]; @@ -24,7 +23,6 @@ static bool read_stdin(std::vector<uint8_t>& data) } return length == 0; } -#endif // Default initialization: Override using a non-weak initialize(). __attribute__((weak)) void initialize() @@ -47,7 +45,6 @@ extern "C" int LLVMFuzzerInitialize(int* argc, char*** argv) } // Generally, the fuzzer will provide main(), except for AFL -#if defined(__AFL_COMPILER) int main(int argc, char** argv) { initialize(); @@ -73,7 +70,6 @@ int main(int argc, char** argv) return 0; } test_one_input(buffer); -#endif return 0; } #endif -
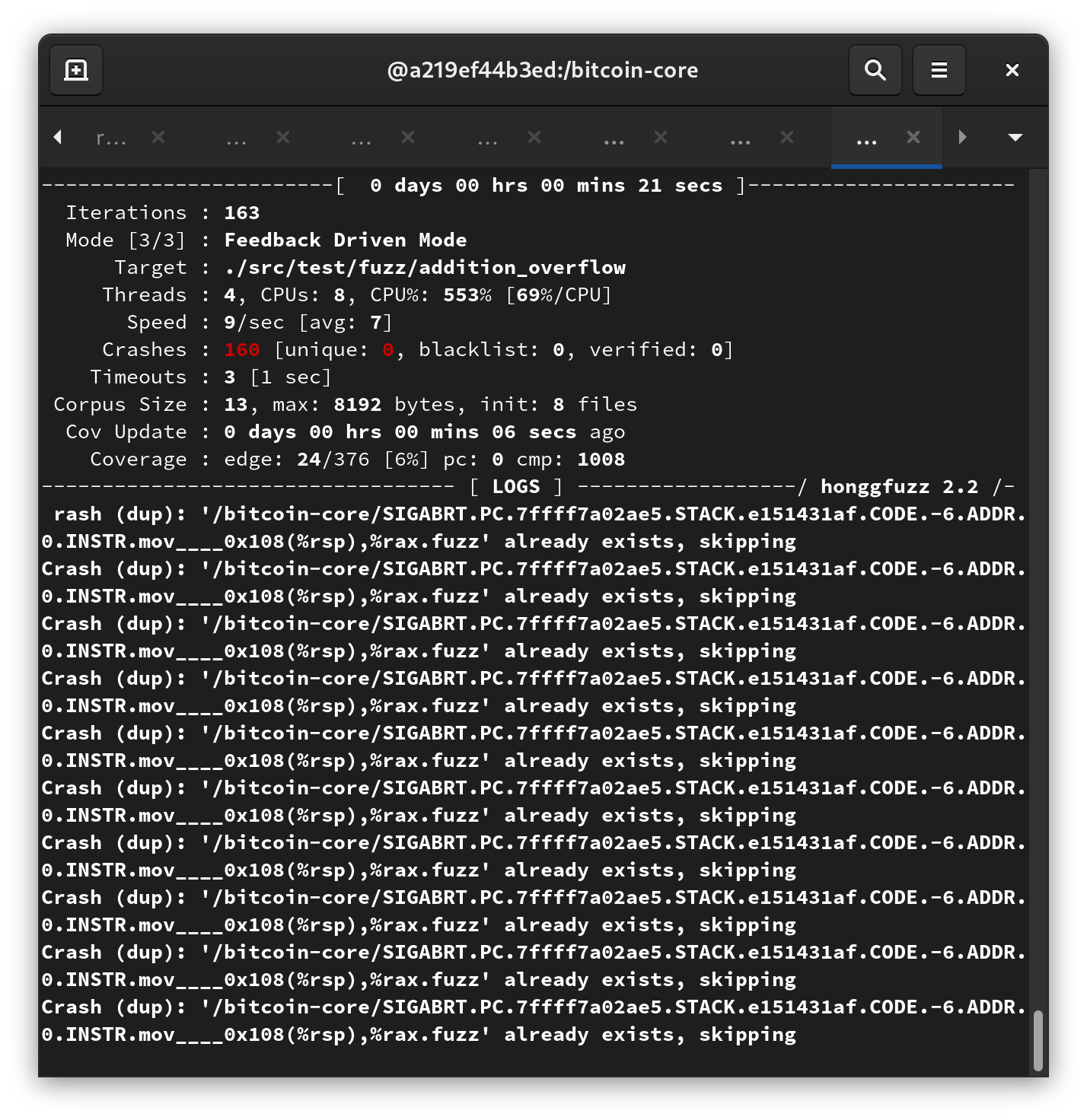
MarcoFalke commented at 5:59 PM on May 19, 2020: member
That works
- practicalswift cross-referenced this on May 19, 2020 from issue Error message "LLVMFuzzerTestOneInput is not defined" also when LLVMFuzzerTestOneInput is defined? by practicalswift
-
practicalswift commented at 6:38 PM on May 19, 2020: contributor
@MarcoFalke Seems like something broke since the instructions were added. Reported upstreams in https://github.com/google/honggfuzz/issues/336 :)
- practicalswift deleted the branch on Apr 10, 2021
- bitcoin locked this on Aug 16, 2022