DNS seed node lookup ambiguous in some (rare) scenarios.
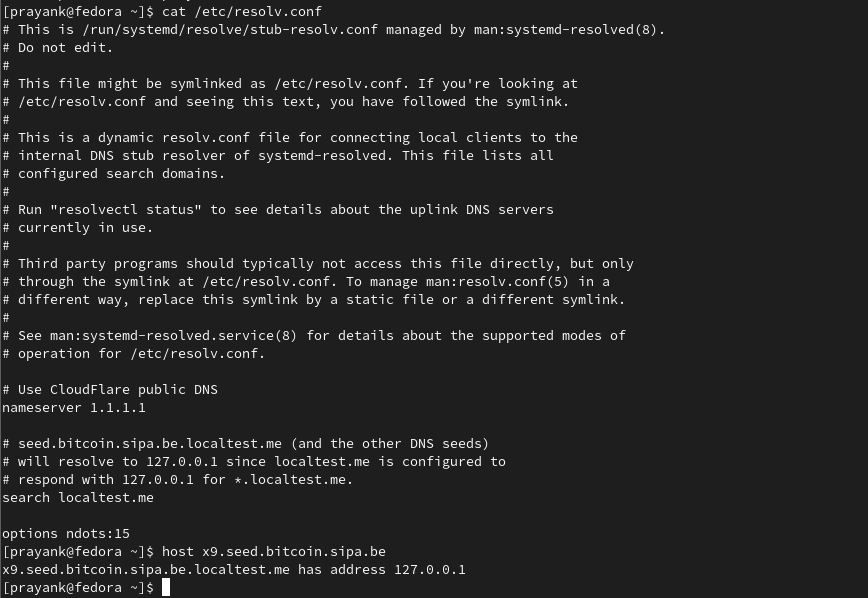
To reproduce run:
$ RES_OPTIONS="options ndots:15" LOCALDOMAIN="localtest.me" src/bitcoind
Context from #22098 (comment):
It is outside of the scope of this PR but I think it would make sense to err on the safe side and specify all seed domain names with an ending dot to make them unambiguous.
In other words …
vSeeds.emplace_back("seed.bitcoin.sipa.be."); // Pieter Wuille, only supports x1, x5, x9, and xd… instead of the current …
vSeeds.emplace_back("seed.bitcoin.sipa.be"); // Pieter Wuille, only supports x1, x5, x9, and xdThe former is guaranteed to be interpreted as
seed.bitcoin.sipa.be.whereas the latter may be interpreted as sayseed.bitcoin.sipa.be.megacorp.com.depending on the content of the user's/etc/resolv.conf.The case I'm thinking about is if
search megacorp.comis specified in/etc/resolv.confand sayoptions ndots:5is used.Looking up
seed.bitcoin.sipa.bewould then result in the following DNS traffic:IP <src> > <resolver>.53: A? seed.bitcoin.sipa.be.megacorp.com. IP <resolver>.53 > <src>: NXDomain IP <src> > <resolver>.53: A? seed.bitcoin.sipa.be. IP <resolver>.53 > <src>: Some valid response.In other words
seed.bitcoin.sipa.be.megacorp.com.would be tried beforeseed.bitcoin.sipa.be.:(
I can think of three different approaches to fixing this:
- Add a
bool allow_non_fqdnargument toLookup*functions, and automatically add a trailing.before passing the hostname string togetaddrinfoif!allow_non_fqdn. This approach would make the choice between FQDN vs "potentially non-FQDN" explicit. I think this is my preferred approach since the caller would explicitly signal his/her intent. - Specify seed node strings as FQDNs by appending
.to the seed hostname strings insrc/chainparams.cpp'svSeed. - Change from
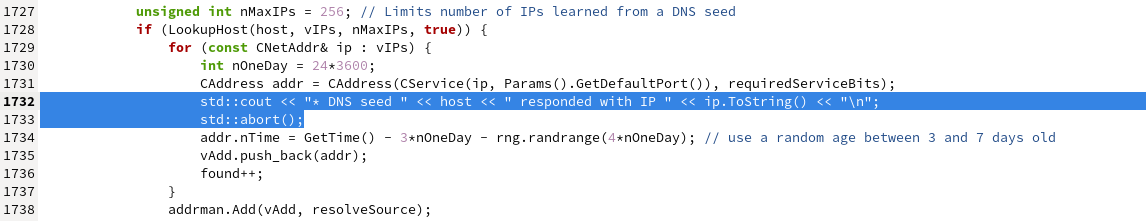
strprintf("x%x.%s", requiredServiceBits, seed)tostrprintf("x%x.%s.", requiredServiceBits, seed)when building the seed hostname inCConnman::ThreadDNSAddressSeed().
Background: #22098 (comment) #22098 (comment) #22098 (comment)